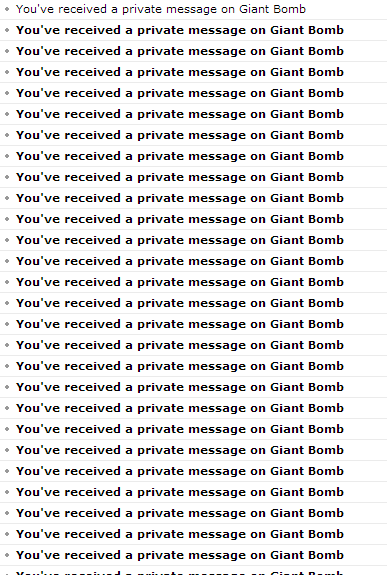
Email bombing is a nasty act when a recipient too many emails are sent to a single email id within a short span. The major reason for using an email bomb is to cramp the target user’s inbox generally sent from a single system. At times, due to this, the mail server stops responding.
After email bombing, you find a huge number of emails suddenly in your inbox. These max out the email attaining limit thus stopping the user from getting further new emails. This results in a situation where the user manually deletes the emails and this takes ample time. See a relevant guide What to do When Your Gmail Account is Full.
Ways used for Email Bombing
Mass Mailing – In this method the bomber delivers the same mail many times to one email id but the spam filters check it easily.
List linking – This is the process of linking an id with subscription links and the receiver keeps on getting subscriptions which you need to delete manually.
Zip Bombing – Here the target receives many Zip files containing characters.
If you want to know the preventive measures to fix Email Bombing then you are at the right place.
Follow a guide – How to Share Large Files on Gmail Using Google Drive.
Methods to fix Email bombing
Proxy Servers
To save yourself from email bombing proxy server is the latest trend in use. A proxy server is one mother computer to which other computers of a specified area are connected. This server has few rules for filtering the information and resources of the computer. And so no unwanted info reaches out to unauthorized people. This helps in stopping suspicious people from knowing the details of your system hence blocking email bombing to a greater extent. So you can use a proxy server to prevent Email Bombing.
Email Filter Applications
You can use a few filter programs available to stop the nuisance spread by the Email Bombs. These email filters are readily available for use. A few filter applications widely used these days are SpamKiller, Spam Buster, ClamWin Free Antivirus, etc.
Simple Mail Transfer Protocol
The method of Simple Mail Transfer Protocol saves a user from the threat of Email bombing. In this process, a user can validate the email transfers with the internet etiquettes. A few agents for the validation of emails are POP or IMAP. Once the device is linked to then SMTP, it checks the email transfer records and also the IP address of the sender. It has the license to reject any message if they are found suspicious.
Closing words
So you see there are a few ways to fix Email bombing. If you follow any of the above methods and be a bit vigilant while operating the device then you can save yourself from the hazards of Email Bombing.
