Microsoft today rolled out the Security Baseline Draft for Windows 10 Version 1809 and Windows Server 2019. This feature will help users secure the OS version in a better way. The file includes Documentation, GP Reports, GPOs, Local_Script, and Templates.
Security baseline Draft for Windows 10 Version 1809 and Server 2019 comes in a downloadable attachment which you can get from the bottom of this page. This has importable GPO, a PowerShell script, custom ADMX files.
Security baseline Draft for Windows 10 Version 1809 and Server 2019 Details
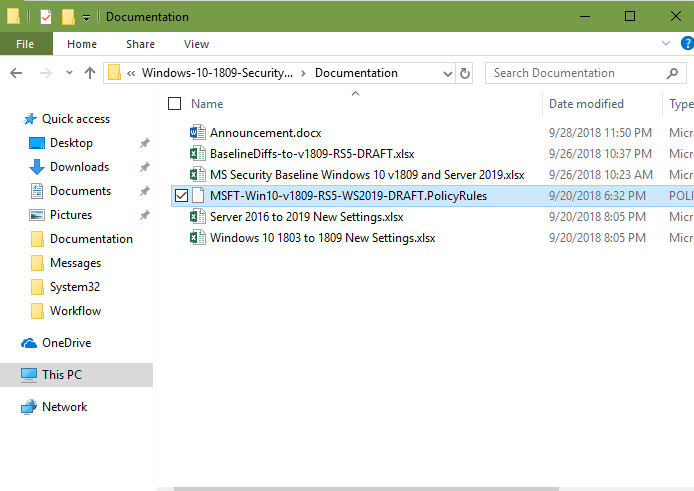
The Security baseline Draft for Windows 10 Version 1809 and Server 2019 includes documentation in .xlsx so see the details of these –
MS Security Baseline Windows 10 v1809 and Server 2019.xlsx
This is multi-tabbed workbook that includes entire Group Policy settings that ship in-box with Windows 10 April 2018 update version and Windows Server 2019 as well. 3 existing Columns Windows 10 v1809, WS2019 Member Server, and WS2019 DC display the recommended options for those scenarios. A few Color-Coded cells mean that these should not be applied to systems that are not joined to an Active Directory domain. Highlighted Cells in the WS2019 DC columns shows the dissimilarity from the corresponding cells in the WS2019 Member Server column. Another change from past spreadsheets is that Microsoft has combined tabs to separate things. Particularly, they are not isolating tabs for Internet Explorer (IE) and Windows Defender AV settings nor the settings for LAPS, MS Security Guide, and MSS (Legacy). All these settings are available now in the Computer and User tabs.
BaselineDiffs-to-v1809-RS5-DRAFT.xlsx
This Policy Analyzer-generated workbook shows the differences in Microsoft security configuration baselines. You will view the comparison between Windows 10 1809 and Windows 10 1803 Settings. Further, you will come to see the difference between Windows Server 2019 and Windows Server 2016 baselines.
Windows 10 1803 to 1809 New Settings.xlsx
The workbook lists all the settings in Windows 10 version 1809 that came since Windows 10 1803.
Server 2016 to 2019 New Settings.xlsx
Lists all the settings that are available in Windows Server 2019 that were added since Windows Server 2016. (We used to highlight these settings in the big all-settings spreadsheets.)
Highlights of the differences from past baselines, which are listed in BaselineDiffs-to-v1809-RS5-DRAFT.xlsx:
- The “MS Security Guide custom setting” safeguarding from potentially unwanted applications has been deprecated in this baseline. You will find these with a new setting under “Computer Configuration\…\Windows Defender Antivirus”.
- Microsoft has enabled the Encryption Oracle Remediation setting in Windows 10 April 2018 update.
They have come with following changes in Virtualization-Based Security settings (Credential Guard and Code Integrity) –
- Platform Security Level changes from “Secure Boot and DMA Protection” to “Secure Boot.” If hardware isn’t compatible with DMA protection, when you will select Secure Boot and DMA Protection it will prevent Credential Guard from operating. So if you accept that your systems support the DMA protection feature, choose the stronger option. Microsoft has opted for Secure Boot (only) in the baseline to minimize the possibility that Credential Guard fails to run.
- Security baseline Draft for Windows 10 Version 1809 and Server 2019 has enabled the System Guard Secure Launch setting on compatible hardware. This changes the method Windows boots to use Intel Trusted Execution Technology and Runtime BIOS Resilience. As a result, it reduces firmware exploits to impact the security of the Windows Virtualization Based Security environment.
- Security baseline Draft for Windows 10 Version 1809 and Server 2019 enabled the Require UEFI Memory Attributes Table option.
- Microsoft enabled the new Kernel DMA Protection feature. The External device enumeration policy manages whether to enumerate the incompatible devices with DMA-remapping. Devices that are compatible with DMA-remapping are always enumerated.
- They Removed the specific BitLocker setting – Allow Secure Boot for integrity validation -because it only enforced a default that was unconvincing to be modified even by a misguided administrator.
- Microsoft eliminated the BitLocker setting – Configure minimum PIN length for startup settings as new hardware features. It reduces the requirement for a startup PIN, and the setting increases Windows’ minimum by only one character.
- They enabled the new Microsoft Edge setting to restrict users from bypassing certificate error message.
- Microsoft cleared the block for handling PKU2U authentication requests, as the need for the feature was increasing.
- They Removed the configuration of Create symbolic links user rights assignment.
- Microsoft eliminated the deny-logon restrictions against the Guests group as it was quite demanding By built-in setting, the Guest account is the only member of the Guests group, and the Guest account is disabled. Only an administrator has the capability to enable the Guest account or add members to the Guests group.
- Microsoft Removed the disabling of the Xbox Game Monitoring Service, as it doesn’t exist in Windows 10 1809.
- They removed the Credential Guard from the Domain Controller baseline. (The feature is not useful on domain controllers
- Microsoft added and enabled a new custom MS Security Guide setting for the domain controller baseline This is Extended Protection for LDAP Authentication (Domain Controllers only). The setting configures the “LdapEnforceChannelBinding” registry value.
- The Server 2019 baselines include all the modifications stored in the 4 Windows 10 releases since Windows Server 2016.
Microsoft has replaced the collection of .cmd batch files with a single PowerShell script. This is applicable to the baselines to the local policy that takes one of these 5 command-line switches to tell which one you want to apply:
.\BaselineLocalInstall.ps1 -Win10DomainJoined - for Windows 10 v1809, domain-joined
.\BaselineLocalInstall.ps1 -Win10NonDomainJoined - for Windows 10 v1809, non-domain-joined
.\BaselineLocalInstall.ps1 -WS2019Member - for Windows Server 2019, domain-joined
.\BaselineLocalInstall.ps1 -WS2019NonDomainJoined - for Windows Server 2019, non-domain-joined
.\BaselineLocalInstall.ps1 -WS2019DomainController - for Windows Server 2019, domain controller
How will you apply BaselineLocalInstall.ps1 script: –
- Make sure that the PowerShell execution policy is configured to allow script execution. You are able to configure the same with the underneath command line –
Set-ExecutionPolicy RemoteSigned - LGPO.exe must exist in the Tools subdirectory or somewhere in the Path. You can download LGPO. from here.
Windows 10 April 2018 update has enhanced its manageability using Mobile Device Management. The Intune team is documenting the MDM security baseline. In addition, Microsoft will publish how to use Intune to implement the baseline very soon.
Download te Security Baselinehe Security Baseline
Security baseline Draft for Windows 10 Version 1809 and Server 2019 holds downloadable attachment holds importable GPO, a PowerShell script, custom ADMX files, documentation in spreadsheet form moreover a Policy Analyzer file (MSFT-Win10-v1809-RS5-WS2019-DRAFT.PolicyRules).
Source – Technet blog.
